What happens if you connect a Windows XP PC without any protection
Imagine connecting an old computer, with Windows XP, to the Internet today without any protection. It’s like leaving your front door wide open and waiting for anything to happen. That’s exactly what an expert did to demonstrate the vulnerability of this obsolete operating system.
In just a few minutes, the PC was filled with malicious programs and was completely compromised. The fragility of Windows XP against cyber threats is obvious, and this experiment serves as a clear warning for everyone still using old systems without protection.
Windows XP without protection: an experiment that exploded in 10 minutes
How the test was prepared
The expert Eric Parker created a virtual machine with Windows XP Service Pack 3, but with the firewall disabled and no NAT, assigning it a direct public IP. This way, the computer was completely exposed to the Internet as it would have been two decades ago.
This setup exactly reproduces the original conditions of the early 2000s, when network security was minimally developed and systems were very vulnerable.
Rapid and ruthless infection
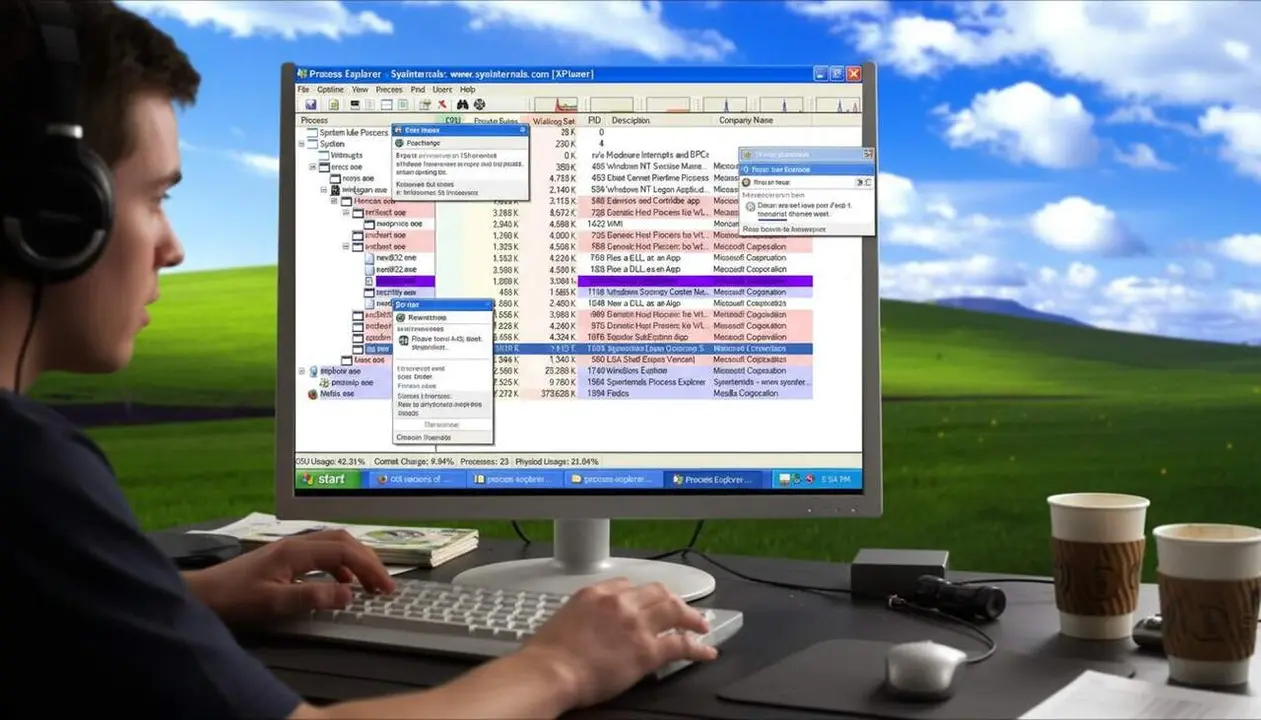
In just 10 minutes, the PC showed clear signs of infection. The process "conhoz.exe," apparently a legitimate component, was actually a Trojan. Later, several types of malware appeared running from temporary folders.
An unauthorized FTP server was also detected that allowed full remote access, DNS modifications to redirect traffic, and the creation of malicious users to maintain control. Altogether, a chain attack that left the system completely hijacked.
The key to the vulnerability: EternalBlue and lack of patches
What is EternalBlue and why is it so dangerous?
EternalBlue is a critical vulnerability present in unpatched Windows XP SP3. This flaw allows attackers to execute remote code without user interaction, opening the door to famous ransomware like WannaCry.
Thanks to this breach, cybercriminals can quickly identify vulnerable machines using tools like Nmap and attack them automatically.
How the risk multiplies without protection
With the firewall disabled and a direct connection, the system becomes an easy target. But even if the firewall and a basic router were maintained, using old browsers and privilege escalation remain serious issues.
For example, the detected malware automatically blocked security tools like Malwarebytes, demonstrating the lack of defenses adapted to these threats.
Windows 7: more resistant, but not immune
The contrast with Windows 7 under equal conditions
To check the difference, the same experiment was performed with Windows 7, under the same conditions. After 10 hours of exposure, the system showed no signs of infection, evidencing the security improvements Microsoft implemented.
This result serves as a reminder that updates are key to protecting information and avoiding massive infections.
What about Windows 10 and the future?
With the imminent end of official support for Windows 10, this test makes us think. If Windows XP is a disaster without protection, Windows 10 also needs to be updated and protected to avoid risks.
Fortunately, today there are many alternatives to avoid being left behind, such as other operating systems or more modern versions of Windows that incorporate better security measures.
| Operating System | Exposure Time | Result |
|---|---|---|
| Windows XP SP3 without protection | 10 minutes | Massive malware infection |
| Windows 7 under the same conditions | 10 hours | No signs of infection |
The reality is that connecting a PC with Windows XP to the Internet without any kind of protection is a direct invitation to attacks. This test is a clear warning for users and companies still relying on these old systems.





